ACTUALLY, OBAMA DIDN'T NEED SUCH AUTHORITY IN 2010...HE ALREADY HAD IT FROM FEDERAL LAWS FROM DECADES AGO, LIKE THIS ONE MORE RE:
Section 606 of the Communications Act of 1934 provides emergency powers to seize control of ALL communications facilities if the president declares there is a "war or threat of war" or "a state of public peril."
EDWARD SNOWDEN REVEALED THE TRUTH IN 2013 IN A SERIES OF INTERVIEWS WITH THE GUARDIAN, U.K.
"Companies like Google, Facebook, Apple, Microsoft– they all get together with the NSA and provide the NSA direct access to the back ends of all of the systems you use to communicate, to store data, to put things in the cloud, and even to just send birthday wishes and keep a record of your life. And they give NSA direct access that they don’t need to oversee so they can’t be held liable for it. I think that’s a dangerous capability for anybody to have but particularly an organization that’s demonstrated time and time again that they’ll work to shield themselves from oversight.
I grew up with the understanding that the world I lived in was one where people enjoyed a sort of freedom to communicate with each other in privacy without it being monitored, without it being measured or analyzed or sort of judged by these shadowy figures or systems anytime they mentioned anything that travels across public lines.
I don’t want to live in a world where everything that I say, everything I do, everyone I talk to, every expression of creativity or love or friendship is recorded. And that’s not something I’m willing to support, it’s not something I’m willing to build, and it’s not something I’m willing to live under. So I think anyone who opposes that sort of world has an obligation to act in the way they can.
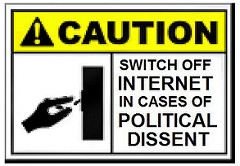
THE WAR TO CONTROL ACCESS TO INFORMATION
WHAT IF OUR ACCESS TO FACTUAL DATA AND TRUTH POSED SUCH A THREAT TO THOSE IN HIGH PLACES THAT THEY HAD DECIDED TO END OUR ACCESS TO IT?
WHAT IF, SLOWLY, SUBTLY, WHAT ONCE WAS 'OUT THERE' FOR US TO FIND AND DIG INTO, TO UNRAVEL AND SEE FOR OURSELVES, WAS JUST GONE, OR REPLACED BY WHATEVER THE TECH GIANTS WANTED US TO FIND AND THAT ONLY?
SOME LONG-TIME READERS WILL RECALL WHEN I JUST DECIDED TO THROW IN THE TOWEL BECAUSE I COULD NO LONGER TRUST ONCE-TRUSTED SOURCES FOR REAL NEWS, HOW I COMPLAINED THAT THE NEWS SOURCES WERE JUST RECYCLING OLD NEWS, WERE CREATING NEWS THAT WASN'T NEWS AT ALL.I FOUND INCREASINGLY "INVALID" LINKS/ERROR MESSAGES TO RECENT AND YEARS-OLD ARTICLES, SOME STILL ACCESSIBLE BY MEANS OF THE INTERNET WAYBACK MACHINE, BUT MOST WERE JUST GONE.
IT SEEMED LIKE, OVERNIGHT, ACCESS TO MANY THINGS WAS CUT OFF.
WELL, IT WAS, AS YOU WILL SEE.
HOW CLOSE DID WE COME TO LOSING UNBRIDLED USE OF THIS INTERNET?
HOW MANY BIG NAMES IN CONGRESS WERE ON THE SIDE OF THOSE WHO WANTED TO THROTTLE WHAT WAS AVAILABLE TO US, TO KEEP ACCESS TO SOME SITES FROM BEING PART OF OUR "FREEDOM OF INFORMATION"?
WHY IS THE U.S. MILITARY PUSHING CONGRESS TO BLOCK SOME SITES FROM OUR SIGHT?
WHY DOES THE MILITARY BLAME OUR ACCESS TO ONCE-INACCESSIBLE INFORMATION AS THE CAUSE OF THE 'REVOLT' OF AVERAGE CITIZENS IN THE LAST ELECTION AND CITIZENS QUESTIONING WHAT OUR 'LEADERS' ARE DOING?
FROM THAT REPORT, ACCESS TO THE INTERNET FOMENTS CIVIL UNREST.
Among the most dangerous drivers of the risk of civil unrest and mass destabilization, the document asserts, are different categories of fact.
“Fact-inconvenient” information consists of the exposure of “details that, by implication, undermine legitimate authority and erode the relationships between governments and the governed”?—?facts, for instance, that reveal how government policy is corrupt, incompetent or undemocratic.
“Fact-perilous” information refers basically to national security leaks from whistleblowers such as Edward Snowden or Bradley Manning, “exposing highly classified, sensitive, or proprietary information that can be used to accelerate a real loss of tactical, operational, or strategic advantage.”
“Fact-toxic” information pertains to actual truths which, the document complains, are “exposed in the absence of context”, and therefore poison “important political discourse.” Such information is seen as being most potent in triggering outbreaks of civil unrest, because it:
“… fatally weakens foundational security at an international, regional, national, or personal level. Indeed, fact-toxic exposures are those likeliest to trigger viral or contagious insecurity across or within borders and between or among peoples.”
WASN'T IT THE INTERNET THAT WAS BLAMED FIRST OF ALL FOR CLINTON'S LOSS IN THE ELECTION?
WASN'T IT "HACKERS, VIA THE INTERNET, WHOM THE DNC AND MAINSTREAM MEDIA BLAMED FOR THE REVEALED TRUTH OF THAT CAMPAIGN'S DIRTY TRICKS AND INTERNAL EMAILS THAT INSULTED JUST ABOUT EVERY GROUP OF PEOPLE IN AMERICA ...EXCEPT THE ELITE?
WASN'T IT THOSE EMAILS "GOING VIRAL" AND OUR ABILITY TO SEE THEM, PLUS THE "VIRAL VIDEOS" THAT SHOWED CLINTON IN FITS OF RAGE, HOW THE CLINTON TEAM WITH HELP FROM THE DNC SCREWED BERNIE SANDERS OUT OF THE NOMINATION, OR SHOWED CLINTON STRUGGLING WITH HER HEALTH THAT TURNED THE TIDE AGAINST CLINTON AND PUT TRUMP IN OFFICE?
LET ME SHOW YOU THE POWER OF THE PEOPLE ON THIS INTERNET.
LET ME SHOW YOU WHY, FOR 100 YEARS AND MORE, THOSE WHO WOULD RULE OVER US HAVE BEEN DEATHLY AFRAID WE WOULD SOMEDAY HAVE THE ABILITY WE NOW HAVE TO SEE THE CHARADE, THE LIES, THE CONS, THE TREASON AND THE COLLUSION OF ALL THOSE ELECTED CRIMINALS, DEMOCRATS AND REPUBLICANS.
THE INSTITUTION OF A "TWO-PARTY SYSTEM" (OR 3 OR 100) WAS FOR ONE THING ONLY...TO DIVIDE THE NATION AND, USING THE ENSUING VIOLENCE BETWEEN THE FACTIONS, STRIP AMERICA AND AMERICANS OF OUR CONSTITUTIONAL RIGHTS AND OUR SOVEREIGNTY.
THEY'VE DONE A GREAT JOB OF THAT...WE'RE ALMOST THERE.
THE INTERNET OFFERS US INCREDIBLE KNOWLEDGE, AN INSIGHT INTO EVENTS AS THEY HAPPEN, CONTACT WITH OTHERS ALL ACROSS THE WORLD IN SECONDS.
IT IS TOO POWERFUL A TOOL FOR "COMMON MAN", SAID OUR MILITARY'S REPORT RECENTLY.
ONCE WE REALIZED WHAT WE HAD, A WAY AROUND THE SPOON-FED GARBAGE OFFERED BY MAINSTREAM MEDIA (MSM), A WAY TO GO STRAIGHT TO THE SOURCES, EVEN ON THE OTHER SIDE OF THE GLOBE, AND SEE THE LIES, SEE THE TRUTH FOR OURSELVES, THE POWERS THAT BE PANICKED LIKE NEVER BEFORE.
EXAMINING THIS FACT, AND THE TERROR THAT TRUMP APPARENTLY STRIKES IN THE ROTTED HEARTS OF THE OWNERS OF THE "GREAT AMERICAN PROPAGANDA MACHINE", SOMETHING HE COULD RELEASE TO THE PUBLIC AT ANY MOMENT, MAYBE YOU WILL SEE WHY THOSE WHO DON'T WANT THAT KIND OF POWER IN THE HANDS OF THE "COMMON MAN", LOWLY US, WE, THE PEOPLE, ARE GOING TO DO ALL THEY CAN TO ROB US OF THIS TOOL WE HAVE THAT UNCOVERS THEIR SCHEMES AND THEIR LIES.
[I will TRY to refrain from ALL-CAPS but no promises.]
FORBES MAGAZINE ONLINE, DEC. 2, 2016
In an op-ed for the Christian Science Monitor, Timothy Edgar, the academic director of law and policy at Brown University's Executive Master in Cybersecurity program wrote,
The view that the internet should be open, interoperable, and free from state censorship has been a pillar of American policy since the 1990s. Mr. Trump sharply departs from this establishment consensus. "We’re losing a lot of people because of the internet," he mused at a rally in South Carolina last year, referring to the online recruitment efforts of terrorist groups. "We have to talk ... about, maybe in certain areas, closing that internet up in some way."
If Trump decides to build a great firewall, he may not need Congress. Section 606 of the Communications Act of 1934 provides emergency powers to seize control of communications facilities if the president declares there is a "war or threat of war" or "a state of public peril." In 2010, a Senate report concluded that section 606 "gives the President the authority to take over wire communications in the United States and, if the President so chooses, shut a network down." With a stroke of a pen, Trump could invoke it.
If Trump wants to “close that internet up,” all he will need is an opinion from his Attorney General that section 606 gives him authority to do so, and that the threat of terrorism is compelling enough to override any First Amendment concerns.
[WRONG, FORBES.
THAT AUTHORITY WAS HANDED TO EVERY PRESIDENT BEFORE , BEFORE COMPUTERS/INTERNET, SINCE 1934 TO CONTROL NEWS SOURCES AND COMMUNICATIONS.
(FEMA sprang forth from the Federal Civil Defense Administration (FCDA) by President Harry S. Truman in 1950.)
EVER SINCE FEMA CAME TO BE, 1978-1979, FEDERAL LAW GIVES TOTAL CONTROL OF COMMUNICATIONS AND TRANSPORT COMPANIES, HIGHWAYS, PORTS, RIVERS, THE AIR SPACE OVER THE U.S., BANKS, ALL LAW ENFORCEMENT AGENCIES, ENERGY COMPANIES, EVERYTHING TO FEMA IN CASE OF "NATIONAL EMERGENCY".
FEMA CAN EVEN SUSPEND THE CONSTITUTION AND SEND CONGRESS HOME FOR 6 FULL MONTHS, NO RECOURSE.
FEMA CAN, DID, AND WILL COMMANDEER THE INTERNET AND PHONE SERVICES FOR THEMSELVES, "IN THE NAME OF NATIONAL SECURITY" OR NATURAL DISASTERS.
AS I WROTE IN AN OLDER ARTICLE ABOUT THE POWER FEMA WIELDS, IT WAS SUPPORTED BY EVERY ADMINISTRATION SINCE TRUMAN.
It was conceived during the Richard Nixon Administration, refined by President Jimmy Carter, then given teeth in the Ronald Reagan and George Bush Administrations.
NOT ONE DAMNED THING WE CAN DO ABOUT IT SHORT OF FULL-BLOWN REVOLUTION, BUT FEMA WILL ALSO CONTROL THE NATIONAL GUARD, WHILE MOST OF OUR ENLISTED MILITARY SERVES ABROAD.
WE'D BE LIKE THE OLD 'INDIANS', OUT-GUNNED.
THERE ARE SEVERAL FAIRLY RECENT INSTANCES IN WHICH BOTH INTERNET AND PHONE SERVICE WERE INTENTIONALLY DISRUPTED DURING PROTESTS AND SO-CALLED DISASTERS.]
In 2010, a Senate report concluded that section 606 "gives the President the authority to take over wire communications in the United States and, if the President so chooses, shut a network down."
Let's not forget Independent Party Senator Joseph Lieberman's 2010 attempt to create an "Internet kill switch" for the President.
The kill switch is associated with S.3480, The Protecting Cyberspace as a National Asset Act [PDF], which was co-sponsored by Senator Joseph Lieberman (I-CT), Senator Susan Collins (R-ME), and Senator Tom Carper (D-DE). The bill, which was first introduced in June 2010, has come under fire for supposedly giving the President the ability to do what Egypt did last week–i.e. cut off the nation’s connection to the rest of the Internet during a time of crisis.
[MY NOTE: Actually, during the Arab Spring in Tunisia, Egypt, and Libya access to the Internet was denied in an effort to limit "peer networking" which protesters were using to organize resistance against those governments.
Looks like our 'Boyz on the Hill', our OWN government are afraid of the same thing HERE in America?]
Joe Lieberman was passionate about the president having the say-so for the kill switch.
In an interview on June 20, 2010, Lieberman said ,
"We need the capacity for the president to say, 'Internet service provider, we’ve got to disconnect the American Internet from all traffic coming in from another foreign country'. Right now, China, the government, can disconnect parts of its Internet in case of war. We need to have that here, too."
[THAT'S NICE, COMRADE LIEBERMAN.]
In June 2016, the U.S. Court of Appeals for the D.C. Circuit upheld the FCC’s power to impose “net neutrality” rules.
ALSO IN 2016: Turkey introduced an internet kill switch law permitting authorities to "partially or entirely" suspend internet access due to wartime measures, national security or public order.
THE UK HAS ADMITTEDLY HAD THIS ABILITY TO KILL THE INTERNET SINCE 2003.
In the United Kingdom, the Communications Act 2003 and the Civil Contingencies Act 2004 allow the Secretary of State for Culture, Media and Sport to suspend Internet services, either by ordering Internet service providers to shut down operations or by closing Internet exchange points.
India frequently terminates internet connections in Kashmir and northeastern states.
SINCE ALL OF THE ABOVE NATIONS HAVE HAD AND USED THE TECHNOLOGY TO LIMIT OR SUSPEND THE INTERNET IN THEIR NATIONS, DARE WE IMAGINE THE U.S. DOES NOT HAVE THIS CAPABILITY?
OF COURSE WE DO!
AS WE'VE SEEN, BACK IN 2016, FORBES WAS ALMOST HYSTERICAL WHEN IT WROTE THE ARTICLE I QUOTED ABOVE WARNING THAT TRUMP COULD KILL THE INTERNET.
BUT IN 2013, WHISTLEBLOWER EDWARD SNOWDEN SAID THAT SWITCH WAS ALREADY THERE.
Snowden gave an interview with journalist Glenn Greenwald about his thoughts on his reasons behind whistleblowing and what what his experience in the NSA was like.
Greenwald: "Talk a little bit about how the American surveillance state actually functions. Does it target the actions of Americans?"
Snowden: "NSA and intelligence community in general is focused on getting intelligence wherever it can by any means possible. It believes, on the grounds of sort of a self-certification, that they serve the national interest. Originally we saw that focus very narrowly tailored as foreign intelligence gathered overseas."
"Now increasingly we see that it's happening domestically and to do that they, the NSA specifically, targets the communications of everyone. It ingests them by default. It collects them in its system and it filters them and it analyses them and it measures them and it stores them for periods of time simply because that's the easiest, most efficient, and most valuable way to achieve these ends. So while they may be intending to target someone associated with a foreign government or someone they suspect of terrorism, they're collecting you're communications to do so."
"Any analyst at any time can target anyone, any selector, anywhere. Where those communications will be picked up depends on the range of the sensor networks and the authorities that analyst is empowered with. Not all analysts have the ability to target everything. But I, sitting at my desk, certainly had the authorities to wiretap anyone from you or your accountant to a Federal judge to even the President if I had a personal e-mail."
Snowden: "The greatest fear that I have regarding the outcome for America of these disclosures is that nothing will change. People will see in the media all of these disclosures. They'll know the lengths that the government is going to to grant themselves powers unilaterally to create greater control over American society and global society. But they won't be willing to take the risks necessary to stand up and fight to change things to force their representatives to actually take a stand in their interests."
"And the months ahead, the years ahead, it's only going to get worse until eventually there will be a time where policies will change because the only thing that restricts the activities of the surveillance state are policy.
And because of that a new leader will be elected, they'll find the switch, say that 'Because of the crisis, because of the dangers we face in the world, some new and unpredicted threat, we need more authority, we need more power.' And there will be nothing the people can do at that point to oppose it. And it will be turnkey tyranny."
I DON'T CARE IF YOU LOATHE SNOWDEN, TRUTH IS TRUTH, NO MATTER WHO TELLS IT.
NEVER HATE THE TRUTH BECAUSE OF WHO TELLS IT.
The US Government Has an Internet Kill-switch — and It’s None of Your Business
[IN 2016], the Supreme Court declined to hear a petition from the Electronic Privacy Information Center (EPIC) that sought to force the Department of Homeland Security to release details of a secret “killswitch” protocol to shut down cellphone and Internet service during emergencies.
The American people are (once again) left in the dark regarding the inner-workings of another dangerous and intrusive government program.
EPIC has been fighting since 2011 to release the details of the program, which is known as Standard Operating Procedure 303.
EPIC writes, “On March 9, 2006, the National Communications System (‘NCS’) approved SOP 303, however it was never released to the public. This secret document codifies a ‘shutdown and restoration process for use by commercial and private wireless networks during national crisis.’”
EPIC continues, “In a 2006-2007 Report, the President’s National Security Telecommunications Advisory Committee (‘NSTAC’) indicated that SOP 303 would be implemented under the coordination of the National Coordinating Center (‘NCC’) of the NSTAC, while the decision to shut down service would be made by state Homeland Security Advisors or individuals at DHS. The report indicates that NCC will determine if a shutdown is necessary based on a ‘series of questions.’”
Despite EPIC’s defeat at the hands of the Supreme Court, the four-year court battle yielded a heavily redacted copy of Standard Operating Procedure 303.
The fight for transparency regarding SOP 303 began shortly after a Bay Area Rapid Transit (“BART”) officer in San Francisco shot and killed a homeless man named Charles Hill on July 3, 2011.
The shooting sparked massive protests against BART throughout July and August 2011. During one of these protests, BART officials cut off cell phone service inside four transit stations for three hours.
This kept anyone on the station platform from sending or receiving phone calls, messages, or other data.'
A MOTHER JONES ARTICLE FROM 2013:
The Government’s Secret Plan to Shut Off Cellphones and the Internet, Explained
"There are a few ways the federal government could exercise its power to shut down and restore internet and cellphone service... The government is explicitly authorized to target a “localized area”—such as a bridge—or potentially an “entire metropolitan area,” according to a recent Government Accountability Office report.
(Both DHS and the White House declined to comment for this article.)
[I]n Egypt, the government spent a lot of time prior to the anti-Mubarek protests making sure all of the nation’s internet service providers ran through a single entryway, so that it could easily shut things off. China is working on nationalized routing.
Harold Feld, vice president at Public Knowledge, an advocacy group focused on communications and technology policy, says that big internet companies still control a large portion of [internet] subscribers in the United States, and if the top 10 service providers cooperated with the government, “you could shut things down fairly easily.”
“I find it hard to imagine why an internet kill switch would ever be a good idea, short of some science fiction scenario wherein the network comes alive a la Terminator/Skynet,” Feld says. “At this point, so much of our critical infrastructure runs on the internet that a ‘kill switch’ would do more harm than anything short of a nuclear strike. it would be like cutting off our own head to escape someone pulling our hair.”
The same argument applies to smothering cellphone service.
“The benefit of people being able to communicate on their cellphones in times of crisis is enormous, and cutting that off is in and of itself potentially very dangerous,” argues Eva Galperin of the Electronic Frontier Foundation.
Is it legal for the Obama administration to activate a kill switch?
Yep, and kill switches aren’t new.
In 1918, a congressional joint resolution authorized the president to assume control of US telegraph systems, in order to operate them during World War I.
Then, in 1934, President Franklin D. Roosevelt signed the Communications Act, which decreed, “Upon proclamation by the President that there exists war or a threat of war, or a state of public peril or disaster or other national emergency, or in order to preserve the neutrality of the United States, the President, if he deems it necessary in the interest of national security or defense, may suspend or amend” both wireless radio and phone services, which means it’s not clear whether this could apply to internet service (although the Federal Communications Commission has used that argument before, when deregulating internet service over telephone lines in 2005).
What is clear is that in 2006, the Bush administration entered into a secret agreement with telecom giants and came up with a specific plan as to when and how the government can actually shut down these networks—called Standard Operating Procedure (SOP) 303.
And in 2012, President Obama reaffirmed that DHS could seize private facilities and shut down communications, in a July executive order.
THERE WAS A KILL SWITCH ON CELL PHONE SERVICE 12 YEARS AGO, FOR SURE.
In 2005, shortly after suicide bombers attacked the London tube, federal authorities disabled cell networks in four major New York tunnels. The action was reportedly taken to prevent bomb detonation via cellphone, and according to a National Security Telecommunications Advisory Committee review, it “was undertaken without prior notice to wireless carriers or the public.”
In 2009, during Obama’s inauguration, the feds used devices that blocked cellphones from receiving signals to prevent bomb detonation. In 2011, officials for the San Francisco transit system cut off cellphone service in four Bay Area Rapid Transit stations for several hours to preempt a planned protest over BART police fatally shooting a homeless man.
What are the constitutional problems of a kill switch?
Civil liberties advocates argue that kill switches violate the First Amendment and pose a problem because they aren’t subject to rigorous judicial and congressional oversight. “There is no court in the loop at all, at any stage in the SOP 303 process,” according to the Center for Democracy and Technology.
“The Executive Branch, untethered by the checks and balances of court oversight, clear instruction from Congress, or transparency to the public, is free to act as it will and in secret.”
David Jacobs of EPIC says, “Cutting off communications imposes a prior restraint on speech, so the First Amendment imposes the strictest of limitations…We don’t know how DHS thinks [the kill switch] is consistent with the First Amendment.” He adds, “Such a policy, unbounded by clear rules and oversight, just invites abuse.”
What don’t we know about the kill switch plan?
A lot.
We don’t know the “series of questions” that help DHS determine whether it should activate a kill switch, how DHS will go about implementing the kill switch, how long a shutdown will last, and what the oversight protocols are.
For example, Jacobs from EPIC says that, it appears that “DHS wouldn’t have to call up the president to implement this, he would be involved in the same indirect way that he is with all kinds of executive branch actions.”
This information was requested in the FOIA lawsuit filed by (EPIC) and could be revealed as early as December. “Hopefully exposure of such a lunatic idea will allow the public to beat some common sense into these agencies,” says Feld.
AND, AS WE SAW ABOVE, EPIC WAS HANDED SUCH A HEAVILY REDACTED, FRAGMENTED PIECE OF THIS THING THAT IT IS BASICALLY WORTHLESS EXCEPT TO LET US KNOW A KILL SWITCH EXISTS FOR CELL PHONE SERVICE.
2016, PROTESTERS IN OREGON HAD BOTH CELL PHONE AND INTERNET SERVICE "KILLED".
It is possible that the government may have used the internet kill switch again, during the standoff at the Malheur National Wildlife Refuge in Oregon in 2016.
On Sunday, January 31st, 2016, Oregon Public Broadcasting (OPB) interviewed David Fry, one of four remaining occupiers at the time, who told OPB that, “the FBI made it so the occupiers can’t make outgoing calls on their cellphones,” and that only his cell phone, “can receive incoming calls, but that the other three in the refuge appear unable to receive calls on their cellphones.”
The occupiers also told OPB that they had lost access to the internet.
According to TheCount.com, “Supporters who attempt to call Fry end up reaching the FBI instead.”
More recently the cellular internet killswitch may have been engaged during the Dakota Access Pipeline protests at Standing Rock in North Dakota.
In one video posted to Facebook in early December 2016 by anti-DAPL activist Josh Long, phones are shown being shutoff, one phone is shown going from fully charged to a drained battery state, and another phone that was halfway charged then became drained as well. Some protesters claim their phone’s GPS function was switched on while at the protest.
Other protesters reported the tell-tale signs of an IMSI catcher being in the area, such as a change in signal strength, or the network being degraded from LTE to 2G. Others claimed their phones had malware installed on them while at Standing Rock.
The North Dakota Air National Guard does have a General Atomics MQ-1 Predator drone stationed at it’s base in Fargo, North Dakota.
The Predator drone can be loaded with equipment to surveil and jam cellular signals, The Intercept has a list of PGL Payloads that can be placed on a Predator drone.
Some aircraft flying over Standing Rock have been using fake tail numbers, including one that was identified as a private helicopter being flown to support law enforcement efforts. It is possible DRT boxes may have been aboard these aircraft.
Non-profit organizations and even a federal agency are investigating the possible illegal use of IMSI catchers at Standing Rock.
The National Lawyers Guild and the American Civil Liberties Union (ACLU) filed a federal Freedom Of Information Act (FOIA) request and a state Open Records Request on October 20th, 2016 to investigate the use of unconstitutional surveillance.
John Wathen, a photojournalist who was at Standing Rock, told the Huffington Post that he had been interviewed by an investigator from the FCC and that, “The FCC has opened an investigation into the use of “Stingray” technology against Water Protectors.”
The Internet Was Just Taken Over by a Global Monopoly, And No One Even Noticed
The U.S. fulfilled its objective to “privatize” the Internet. September, 2016
Some U.S. lawmakers felt giving up oversight could permit less scrupulous regimes to seize total or partial control of vital Internet function — with potentially disastrous results.
The Chicago Tribune quoted Ted Cruz: “President Obama intends to give increased control of the Internet to authoritarian regimes like China, Russia, and Iran. Like Jimmy Carter gave away the Panama Canal, Obama is giving away the Internet.”
And as The Economist noted, whoever controls the Internet’s “address book” also holds the power to censor — any domain name can be revoked and the website no longer found.
Critics have also noted the eagerness of proponents of the transition as an indicator ceding control should be considered more carefully — or at least delayed significantly to give the American public some say in the matter."
'PREVENT INTERNET PRIVACY FOR 'COMMON CITIZENS' AT ANY COST.'
THIS REALLY BACKFIRED ON CLINTON, DIDN'T IT, WHEN WHAT SHE THOUGHT WAS PRIVATE TURNED OUT TO BE A 'VIRAL SENSATION' THANKS TO WIKILEAKS.
December 20, 2015
Hillary Clinton’s response to a question about the power of high technology to ensure privacy.
Blasting “encrypted communication that no law enforcement agency can break into,” Clinton said, “I would hope that, given the extraordinary capacities that the tech community has and the legitimate needs and questions from law enforcement, that there could be a Manhattan-like project...
Tech companies like Apple have resisted calls to place a “backdoor” in encryption technology that would allow governments to peek at private communications, arguing that such a backdoor could equally be exploited by hackers and render the privacy protections useless.
“Maybe the backdoor is the wrong door, and I understand what Apple and others are saying about that,” Clinton said, insisting nonetheless that a door was necessary: “I know that law enforcement needs the tools to keep us safe.”
Aaaaaaaaand Hillary just terrified everyone with an internet connection. #DemDebate
— Edward Snowden (@Snowden) December 20, 2015
That is when the tech giants started stepping in, because if the media could no longer control the masses with their propaganda, tech giants like Google, Facebook, Twitter, YouTube (owned by Google), and others, could damn well control what was and wasn't seen on the Internet.
Facebook framed it as a battling "fake news" on their platform, after denying that "fake" stories had any impact.
Twitter started censoring and shadow-banning conservative voices from sharing content, claiming certain content was "sensitive content."
YouTube started flagging channels on restricted mode, start demonetizing videos with claims of fighting "extremism."
Google, the largest search engine on the net, has started making sure the "results" found during searches were their preferred narrative versus items that actually ranked higher, providing higher ranking (seen on the 1st page of their search results) to leftist sites like Snopes, Wikipedia, and the mainstream media , with few exceptions.
The difference between searches on Google and the results found, compared to DuckDuckGo, is amazing.
THE EFFECTS OF THIS COORDINATED CAMPAIGN CAN BE SEEN IN THE NUMBERS
Independent Media website owners can tell readers all day long how this has effected not just traffic but revenue as the MSM, and now the tech giants, have all started waging war on Independent Media, but seeing is believing, so we conducted an experiment using Alexa, which is a site that analyzes website traffic and statistics, and the results, seen in graphs, for a large number of Independent Media sites, provides indisputable proof of how effective their coordinated campaign has been.
“Google has an 88 percent market share in search advertising, Facebook (and its subsidiaries Instagram, WhatsApp and Messenger) owns 77 percent of mobile social traffic and Amazon has a 74 percent share in the e-book market,” University of Southern California Annenberg Innovation Lab director emeritus Jonathan Taplin wrote in an April 22 op-ed in the New York Times.
“In classic economic terms, all three are monopolies.”
High-profile journalist Glenn Greenwald, who won a Pulitzer Prize for his reporting on National Security Agency spying on Americans (revealed in leaks by Edward Snowden) tweeted April 22 that a discussion on the tech firms’ market domination was “way overdue.”
“The unrestrained power amassed by the Silicon Valley monopolies is staggering,” Greenwald tweeted.
Greenwald is not the only one that has suggested this, as top White House adviser Steve Bannon, has also been arguing for it and the question of breaking up Google was even argued at the liberal NYT.
May be the first (and last!) time in history that Steve Bannon and any writer at the NYT actually agree on anything.
THE BATTLE FOR THE INTERNET
Most people in this country have access to at most two broadband providers. This lack of competition gives those providers control over consumers’ access to internet services and content – as well as internet companies’ access to those same consumers.
Most broadband providers are also cable and telephone suppliers and offer services that compete with those internet companies. For example, Netflix competes with cable companies’ various programming offerings, such as on-demand programming and streaming video services. There is an obvious incentive for the broadband provider to degrade or block Netflix service. Alternatively, the provider could extract additional payment not to do so.
Major sections of the FCC’s first network neutrality rules were struck down last year by a federal court of appeals. The key issue was not the wisdom of the rules, adopted in 2010, but the authority of the FCC to implement them.
The FCC had classified broadband providers as “information services” rather than “telecommunications services.”
Information services are subject to limited regulation.
In contrast, telecommunication services are subject to substantial regulation under Title II of the Communications Act.
There is also the possibility that Congress may step in and pass net neutrality regulation limiting the FCC’s authority to impose its own rules or creating a different set of them.
In general, Democrats, who are the majority on the FCC, favor net neutrality, while Republicans, the majority in both houses of Congress, oppose it.
The FCC is forced to regulate 21st-century technology with 20th-century law. The last major rewrite of the Communications Act was pre-broadband, long before Facebook and YouTube even existed. Even Google was a year away. The long-term solution is a complete rewrite of the Communications Act, but that appears unlikely anytime soon.
AS ALWAYS, THERE IS NOTHING NEW UNDER THE SUN AND THE SITUATION AMERICANS ARE IN TODAY WAS FORESEEN AND WRITTEN ABOUT ALMOST 50 YEARS AGO BY A VERY DANGEROUS MAN.
THE SURVEILLANCE STATE, THE CONTROL OF ALL WE CAN FIND AND READ OR SEE FOR OURSELVES, INDEPENDENTLY, WAS 'PREDICTED', IF NOT PLANNED, IN 1968 AND 1970.
The inspiration for [David] Rockefeller’s Trilateral Commission was Zbigniew Brzezinski’s 1970 book, 'Between Two Ages'.
Here is a short look at what Brzezinski actually wrote:
"Another threat, less overt but no less basic, confronts liberal democracy. More directly linked to the impact of technology, it involves the gradual appearance of a more controlled and directed society. Such a society would be dominated by an elite whose claim to political power would rest on allegedly superior scientific know-how. Unhindered by the restraints of traditional liberal values, this elite would not hesitate to achieve its political ends by using the latest modern techniques for influencing public behavior and keeping society under close surveillance and control." (Between Two Ages, pp.252-253).
The second source, less well known, is a Brzezinski article “America in the Technetronic Age”, that appeared in the now defunct journal Encounter (January 1968).
What Brzezinski wrote, over forty years ago, is this:
"At the same time, the capacity to assert social and political control over the individual will vastly increase. As I have already noted, it will soon be possible to assert almost continuous surveillance over every citizen and to maintain up-to-date, complete files, containing even most personal information about the health or personal behavior of the citizen, in addition to more customary data. These files will be subject to instantaneous retrieval by the authorities." (p.21).
Brzezinski seemed to believe the “long-range effect” of the “transition and its turmoils” he was documenting would be to “deepen and widen the scope of the democratic process in America” (Between Two Ages, p.265).
ALSO FROM THAT SAME BOOK:
"Today we are again witnessing the emergence of transnational elites … [Whose] ties cut across national boundaries … It is likely that before long the social elites of most of the more advanced countries will be highly internationalist or globalist in spirit and outlook …(p.59) The nation-state is gradually yielding its sovereignty …(p.56) [F]urther progress will require greater American sacrifices. More intensive efforts to shape a new world monetary structure will have to be undertaken, with some consequent risk to the present relatively favorable American position." (p.300).
GOOD CALL, O GLOBALIST TOOL. INSIDER INFORMATION, WAS IT?
TAKING DOWN THE INTERNET WOULD CREATE AN ECONOMIC NIGHTMARE AS THE FOLLOWING PDF SHOWS.
BUT WHAT'S A LOT OF MONEY LOST COMPARED TO CONTROL OF THE MASSES, RIGHT?
(PDF) Dainotti et al., Analysis of Country-wide Internet Outages Caused by Censorship, ACM, 2011
THERE ARE SEVERAL PDFs ABOUT DETECTING THE KILL SWITCH ONCE IT'S INITIATED AND THE SOMEWHAT HOPELESSNESS OF BEING ABLE TO DO ANYTHING ABOUT IT <HERE>.
IT'S A LOT OF READING AND IT ISN'T PLEASANT.
WE'LL ALL JUST AWAKEN ONE DAY, GO TO THESE COMPUTERS, TURN ON AND FIND....NOTHING...IT WILL JUST BE GONE.
THE IDIOTS RIOTING ALL OVER THE NATION AND TRYING TO KILL ONE ANOTHER ARE JUST BRINGING IT ABOUT FASTER THAN WE MIGHT HAVE SEEN IT HAPPEN HAD WE NOT BECOME A NATION OF HATERS WHO HATE HATERS WHO HATE ....WELL, YOU KNOW....
TOUGH TIMES AHEAD, PEOPLE OF EARTH.
ALL THE BEST.
_____________________
BTW....SO THAT WE WHO HAVE INTERNET ACCESS AND HAVE WIKILEAKS ON THE INTERNET DON'T FIND MORE THAN WE "SHOULD", A GREAT PURGE OF DIGITAL RECORDS IS UNDERWAY TO KEEP SECRET MANY, MANY THINGS...
Edward SnowdenVerified account @Snowden Jul 18
"The CIA plans to destroy the records of its investigations into journalism it didn't like."
https://t.co/bLoNPnn2SS
DELETE FILES REGARDING AMERICAN WAR CRIMES...PROTECT LBJ, REAGAN, BUSH JUNIOR, OBAMA, ET AL..
Tillerson to Shutter State Department War Crimes Office
Critics charge top U.S. diplomat with giving the green light to perpetrators of mass atrocities.
Tillerson is downgrading the U.S. campaign against mass atrocities, shuttering the Foggy Bottom office that worked for two decades to hold war criminals accountable, according to several former U.S. officials.
EPA FILES....GOING, GOING, GONE. MUSTN'T HAVE CLIMATE CHANGE EVIDENCE.
ERASING HISTORY IS A PURELY MARXIST GOAL.
LOOK AT WHAT COMMUNISTS DO, WHAT ISIS IS CURRENTLY DOING...ERASE HISTORY.
THAT WAY NO ONE CAN LOOK BACK ON A TIME WHEN THE WHOLE WORLD WASN'T WHAT THE NEW MASTERS WANT IT TO BE.
//WW


No comments:
Post a Comment